Understanding DDoS Attacks
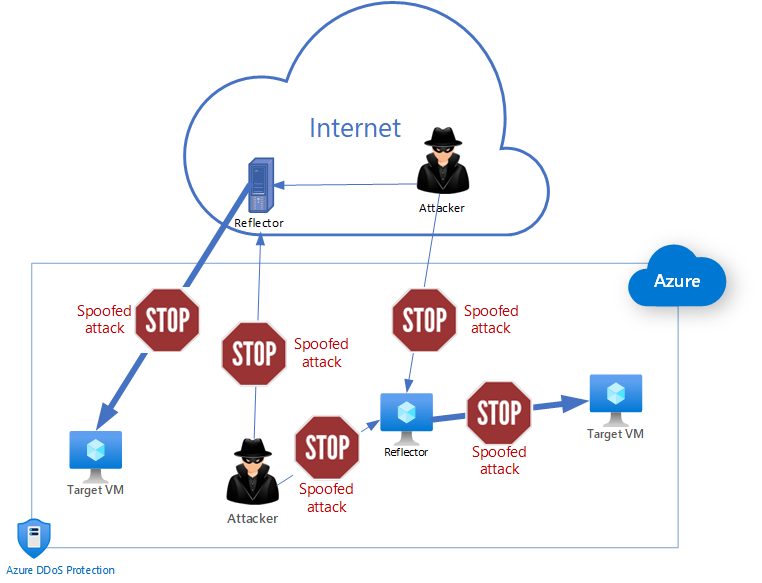
Distributed Denial of Service (DDoS) attacks are orchestrated efforts by malicious actors to disrupt the normal operation of targeted servers, services, or networks. These attacks flood a target’s resources or its supporting infrastructure, often with traffic from thousands of compromised systems, known as a botnet. This massive volumetric surge of traffic is typically meant to exhaust computing resources, bandwidth, and network devices, causing systems to slow down significantly or fail altogether. The consequences can be severe, including lengthy downtime, financial losses due to service unavailability, and permanent damage to brand reputation, particularly if users perceive the organization as ill-prepared to handle such incidents. Proactive organizations often seek specialized DDoS protection services to safeguard their infrastructure and maintain continuous access for legitimate users, leveraging expertise and technology purpose-built to block unwanted traffic surges.
As online operations become central to business strategies, the threat from DDoS attacks grows increasingly significant. Attackers aim to exploit vulnerabilities in outdated software or under-protected network infrastructure, exploit resource limitations, and overwhelm targets to achieve their desired disruption. Attack motivations can range from extortion and hacktivism to simple mischief or as a smokescreen for more covert intrusions happening elsewhere on the network. Understanding the evolving tactics behind these attacks is critical for organizations that rely on constant uptime and digital reliability. Staying informed about the latest attack vectors, such as multi-vector assaults that combine several techniques, is crucial for maintaining effective defense.
Detection: The First Line of Defense
Rapid detection is the linchpin of an effective DDoS defense, as early warnings can greatly reduce the impact of an attack. Modern detection strategies focus on identifying traffic anomalies, such as unexpected spikes, sudden surges from particular IP ranges, or changes in network behavior, that differ from established baselines of normal activity. By integrating continuous monitoring tools and automated alert systems, businesses improve their ability to distinguish between legitimate increases in usage, such as those during sales or special events, and the early signs of a malicious attempt. Early indicators may include customers complaining of slow website performance or critical digital services becoming intermittently unavailable.
These detection methods use advanced analytics, behavioral baselining, and, in some cases, AI-based engines to distinguish true threats from false alarms. Automated security information and event management (SIEM) systems can quickly surface subtle indicators of compromise that human analysts might miss. Automation is especially important due to the speed at which DDoS attacks can escalate, often leaving little room for manual intervention during the early phases. Accelerated detection not only buys valuable response time but can also trigger pre-planned playbooks without delay, helping protect core business functions and sensitive assets.
Analysis: Understanding the Attack
Once a threat is detected, it is essential to analyze its specific characteristics. This analysis includes identifying the attack type—such as volumetric, protocol, or application-layer attacks and mapping the targeted resources and the methods used to generate malicious traffic. For instance, volumetric attacks seek to saturate bandwidth, protocol attacks exploit weaknesses in networking protocols, and application-layer attacks attempt to exhaust application-level resources. These insights help security teams create bespoke responses and prioritize defense efforts where they are most needed, focusing on the most vulnerable or business-critical systems first.
A thorough post-analysis can indicate whether an attack is a one-off or part of an ongoing campaign, providing vital context for allocating resources and updating defenses. Forensic examination of logs and traffic captures can reveal the origins of the attack, the duration of each attack phase, and patterns that could signal future attempts. Understanding attack vectors and infrastructure vulnerabilities helps organizations update their defenses and close security gaps, both in real time and as part of their long-term security improvement plans. Ongoing analysis and forensics not only aid in the current situation but are vital for long-term risk mitigation, helping to refine detection and mitigation strategies with each incident.
[suggestion]A simple diagram showing the lifecycle of a DDoS attack: starting with detection, moving through analysis and mitigation, and ending with recovery, depicted as arrows moving from one stage to the next.[/suggestion]
Mitigation: Implementing Countermeasures
Rate Limiting
Rate limiting is a technique that caps the number of requests a server accepts within a given window, delaying or dropping excess requests. By controlling traffic in this way, organizations prevent their resources from being overwhelmed and maintain service availability for genuine users, ensuring business continuity during an attack. This approach, while effective, must be carefully configured so that it does not inadvertently disrupt access for legitimate users or business partners, which is why adaptive or dynamic rate-limiting mechanisms are often employed. Rate limiting buys valuable time for further analysis and action, providing a buffer while more advanced countermeasures are deployed.
Traffic Filtering
Effective filtering mechanisms differentiate between malicious and legitimate requests. Filtering may be based on IP blacklists, geolocation data, or specific patterns in the attack signatures, such as request headers, payload anomalies, or protocol misuse. Advanced filters may employ machine learning to recognize evolving attack vectors or previously unseen threat actor tactics. By filtering out harmful traffic, organizations can ensure that real users are not blocked by their defensive measures. This balance between strong defense and user accessibility is crucial for maintaining trust and uninterrupted service.
Anti-DDoS Solutions
Deploying purpose-built anti-DDoS appliances or leveraging third-party cloud solutions can effectively absorb and deflect attack traffic. Cloud-based mitigation partners are particularly effective in on-demand scaling and can route malicious traffic away from the organization’s core network infrastructure before it reaches critical systems. Managed DDoS protection solutions provide around-the-clock coverage and can scale rapidly in response to attack volumes, which is especially important for organizations with limited in-house resources. The combination of on-premises and cloud-based tools provides a layered defense, ensuring redundancy and flexibility in mitigation strategies.
Recovery: Restoring Normal Operations
After an attack has been mitigated, it is crucial to move quickly towards restoring normal operations. This begins with assessing the extent of the disruption and damage, then systematically restoring affected systems according to a prioritized restoration plan. Quick recovery is often the result of thorough preparation; organizations with documented, rehearsed recovery processes can efficiently orchestrate system repairs, reboots, or data reconciliations.
Recovery procedures not only involve technical repair work but also communication with stakeholders and customers to maintain transparency and trust. Openly updating users on the cause, duration, and extent of the outage is vital for reputation management. Organizations should use this period to document the attack timeline and compile lessons learned, detailing the strengths and weaknesses of their response. This information can then inform future updates to security policies and recovery procedures, ensuring constant learning and adaptation.
Proactive Measures: Strengthening Defenses
Proactive defense strategies focus on reducing the attack surface and improving the baseline resilience of IT infrastructure. Regular software patching ensures that known vulnerabilities are promptly closed, reducing exploitable entry points for attackers. Establishing network redundancy, such as backup data centers or multiple communication channels, ensures continued operations even during an incident by shifting traffic to unaffected infrastructure. Implementing diversified DNS or load balancing solutions can further help distribute incoming traffic and absorb unexpected surges.
Regular security audits and penetration testing can uncover latent weaknesses before attackers can exploit them, allowing organizations to shore up defenses in advance. These ongoing assessments, combined with up-to-date employee training, strengthen the organization’s overall security posture and readiness for future incidents. Raising security awareness among all staff is often an overlooked yet powerful defense against social engineering tactics that sometimes accompany DDoS campaigns.
Incident Response Planning: Preparing for the Inevitable
Organizations that develop comprehensive incident response plans fare better during and after a DDoS attack. A solid incident response plan clearly defines the roles and responsibilities of key personnel, outlines steps for containing and eradicating threats, and establishes communication protocols for internal stakeholders and external parties such as customers or partners. Well-documented plans minimize confusion, speed up critical decisions, and ensure regulatory and contractual requirements are met during high-pressure scenarios.
Regular simulations and plan reviews ensure that everyone knows what to do when an attack occurs, reducing confusion and delays during a live event. Frequent tabletop exercises and live drills provide valuable opportunities to test the plan’s effectiveness and make improvements based on lessons learned and the latest threat intelligence. The most effective plans are living documents, subject to continuous improvement after every incident and rehearsal, ensuring the organization adapts to new attack methods and organizational changes.
Final Thoughts
The life cycle of a DDoS incident, from detection to recovery, is a critical aspect of modern cybersecurity. Early warning systems, thorough analysis, tailored mitigation strategies, and organized recovery efforts work together to minimize damage and disruption. By prioritizing preparedness through proactive measures and detailed incident response planning, organizations can maintain their operational continuity and safeguard their reputations in an increasingly hostile digital landscape. Ultimately, a strong defense against DDoS attacks not only protects technology infrastructure but serves as a cornerstone of public confidence and business resilience in the digital age.